Exploring @ Webtosociety Com: A New Approach to [Topic/Service]
@ Webtosociety Com – The digital landscape continues to evolve, bringing new platforms, services, and communities that shape how we…
Newznav.com 8884141045 – Everything You Need To Know
Newznav.com 8884141045 – In today’s fast-paced world, staying up-to-date with the latest news and information is more critical than ever….
Thespark Shop Boy & Girl Clothes Online – Complete Guide
Thespark Shop Boy & Girl Clothes Online —Finding the seamless clothes for your little ones can be a delightful but…
How Data Analytics is Reshaping Book Publishing Strategies
The publishing world has always danced between instinct and insight. Editors once trusted gut feelings and hopeful trends to pick…
How to Choose the Right Network Cabling for Business Performance
Networking cabling forms the backbone of any effective business communication process in today’s digital era. The right kind of network…
Techno Mechanicus Musk: The New Addition to Elon Musk’s Family
Techno Mechanicus Musk – Elon Musk, the Tesla chairman and founder of SpaceX and PayPal, is one of the most…
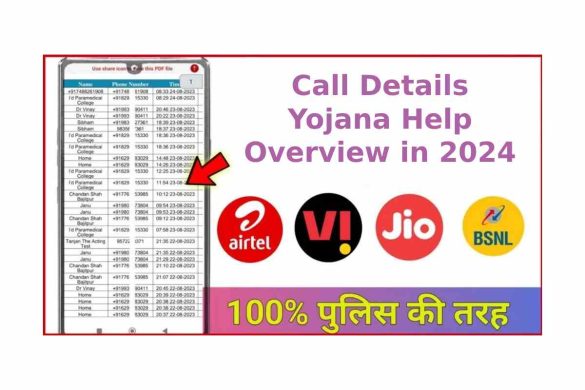
Call Details Yojana Help – Overview in 2024
Call Details Yojana Help Call Details Yojana Help: You can get the call details of any phone number in just…
Adsy.pw/hb5 – The Unique Platform for Digital Success
Adsy.pw/hb5 – Successful businesses depend on visibility, engagement, and trust. These can range from a digital marketer or a content…